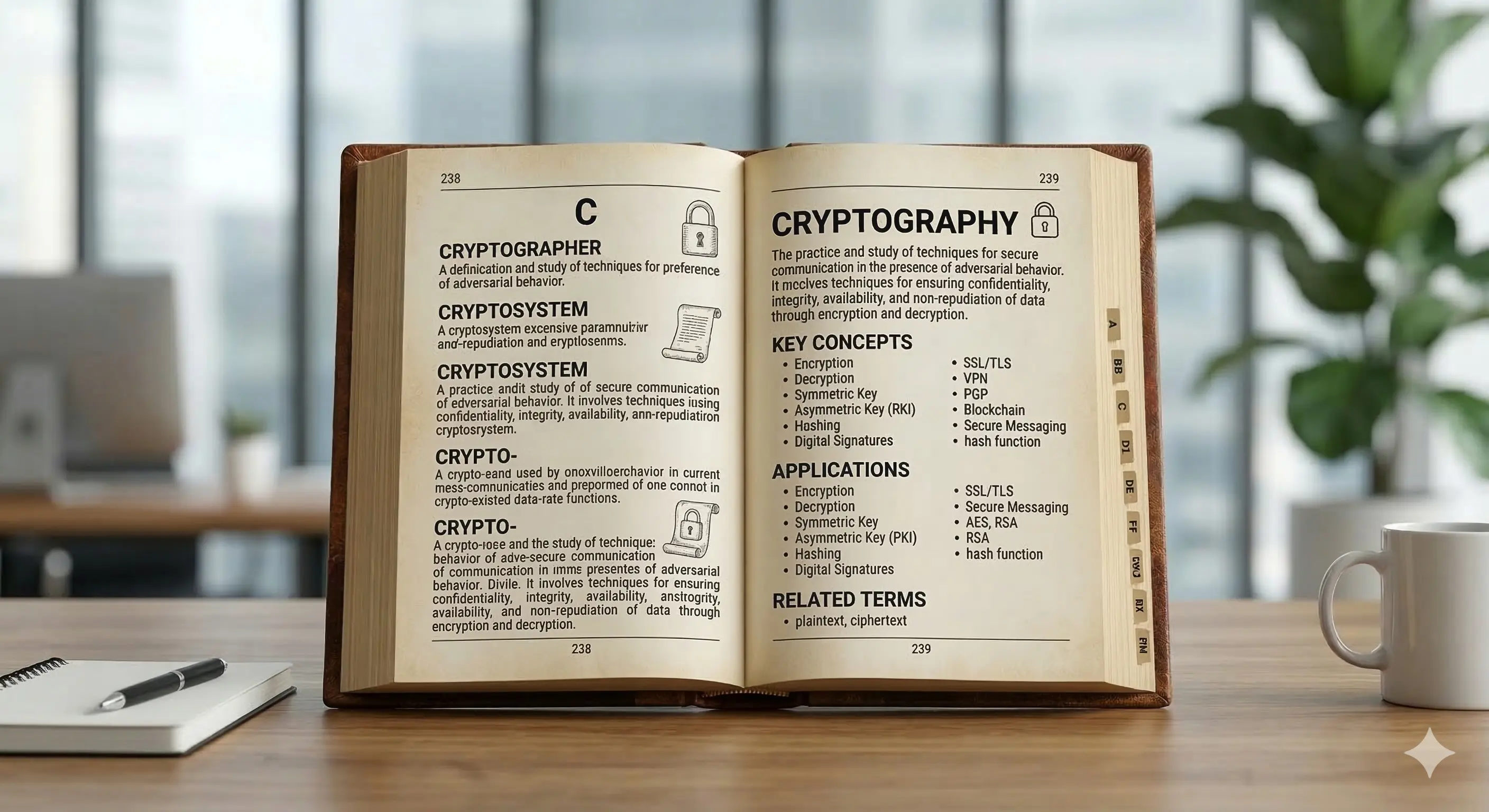
Cybersecurity Glossary: The Language of Digital Protection
100+ key terms every enterprise must master. From phishing to Zero Trust, find clear definitions, practical examples, and the context you need to protect yourself.
Discover how to apply these concepts